The development of compliant information governance policies requires expertise from certified professionals, with practical guidelines developed to meet the needs of your business. Information governance services support organizations in meeting security policies and achieving compliance with a variety of federal, provincial, and industry regulations — including the ability to audit, demonstrate and defend compliance efficiently.
Every transaction between an organization and their stakeholders produces a trail of data. This may be highly sensitive, as with personally identifiable information (PII) or payment card industry (PCI) information, requiring security, privacy, and discovery controls. Other data has no value and simply takes up space, commonly referred to as ROT (redundant, obsolete or trivial) data. It is estimated that ROT data accounts for a minimum of 25-30% of an organization’s data, with other sources saying it can be much higher.
Unstructured data is information that hasn’t been organized into a traditional, structured database format, which means it isn’t accessible, tracked, or leveraged for business insights. Without managing your repository — most of which is unstructured — you’re at risk of storing high quantities of ROT data and exposing your organization to risk and vulnerability if breached.
Unstructured data is a key contributor to security breaches, privacy violations, high IT costs, and compliance penalties. When considering cybersecurity, unstructured data is often the low-hanging fruit cyber criminals will target to gain access to deeper systems. They are looking for things they can monetize, such as names, addresses, dates of birth, social security numbers, passwords, credit card numbers, banking information, or contracts. Unfortunately, this sensitive data is often found throughout the infrastructure, making it difficult to track and keep secured.
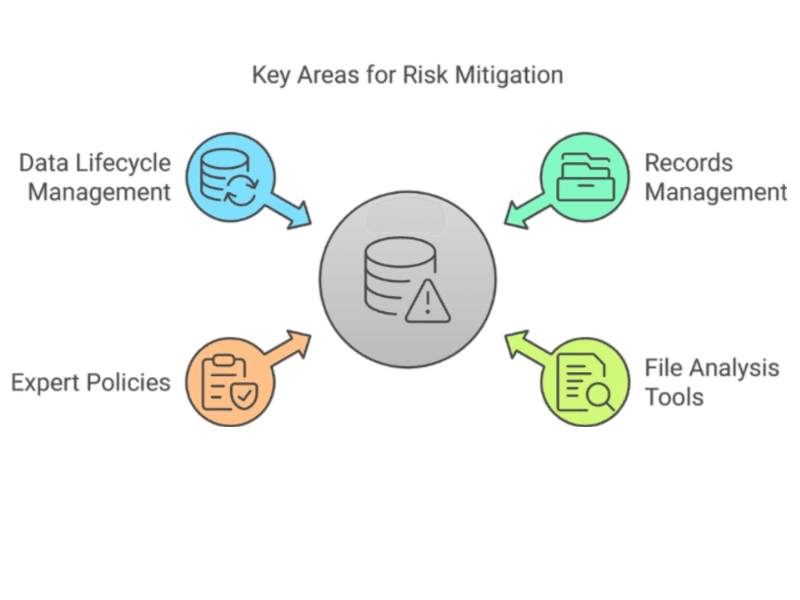
Here are four key areas to mitigate risk through information governance
1. Records and information management program
Implementing a records information management (RIM) program ensures organizations can comply with regulatory and legal requirements while improving efficiency in access to information. Proper RIM practices, supported by a secured platform, help protect information through secure storage, access controls, encryption and audit trails, reducing the risk of security and privacy breaches. It’s essential to establish governance policies, developed with certified records management experts, that encompass information across the organization, supported by practices and technologies that enable governance through the entire lifecycle, from collection to storage to disposition. By doing so, organizations can safeguard against breaches and maintain the integrity and confidentiality of critical data while bolstering trust and reliability.
2. File analysis and classification tools
AI-based technology to categorize or index your documents so the data can then be easily extracted, exported, accessed, and protected. Implementing a system to classify your data can strengthen your security by reducing ROT data assets, proactively managing the lifecycle of your data, and ensuring compliance with privacy regulations. Data discovery also remediates data by restricting access, encrypting, archiving, redacting, or moving sensitive data to secured locations.
It can also transform data generated from various physical and digital workflows into intelligence to enable better decision-making, more responsive customer service, and efficient operations. Ricoh security and process specialists have a deep understanding of information generated from print, mail and digital workflows as well as archiving and email security, so the right approach is applied when classifying your data.
3. Expert-driven policy and implementation
Establishing an information governance policy with leadership-level endorsement provides a structured framework of controls and measures to effectively direct how information is handled. Governance helps mitigate organizational risk and ensures technologies and behaviours comply with legal and regulatory requirements. Once policies and guidelines are put in place, effective data protection procedures can be enacted across people, processes and technologies.
Policies should cover information and records management, privacy controls and data security. Organizational guidelines will set out the procedures, workflows and safeguards through operational manuals and communications, with roles and responsibilities clearly outlined. A regular cadence for training is necessary as operations and regulations evolve. Enabling technologies can be implemented to enact controls, automate processes and measure, track and report outcomes.
4. Data lifecycle management policies and procedures
This security best practice seeks to mitigate an organization’s risk through the management of data, including sensitive and valuable information throughout the entire information lifecycle. Ricoh professional services and managed services teams can assist in any step of this process. Retention and disposal policies and procedures determine the lifecycle and handling of different classes of data.
Retention policies can determine when and how data is moved from your active repositories into an archived state, moved into an off-site cloud repository, or expunged from systems as warranted by policy. Services for end-of-life disposal encompass cleansing data from multifunction devices to ensure that the NVRAM and drives of retired customer devices are wiped clean before disposal.
Business process automation
- 1IDC. “High Data Growth and Modern Applications Drive New Storage Requirements in Digitally Transformed Enterprises,” July 2022.