Summary
Many organizations have embraced hybrid work as a permanent way of working and this shift brings unique challenges and complications in the retention and preservation of electronically stored information (ESI).
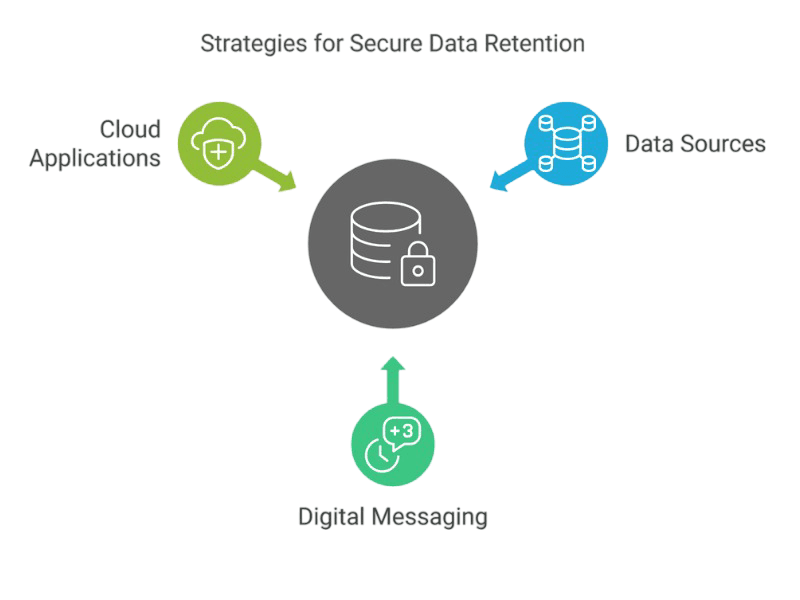
Understand where your data is coming from
Consider conducting a regular review of systems and applications that your organization’s employees are using, and the various data formats created and stored. By doing so, you are creating a valuable record of how your organization acquires, uses, stores and shares data – providing a useful resource whenever the need arises. It also creates a foundation for building a data protection strategy and retention guidelines to reduce your organization’s security and legal risks.
Developing an understanding of the technology and systems in use within your organization also allows you to identify areas for improvement to better support your hybrid workforce – enabling you to be proactive in adopting new communication and collaboration technologies to meet their needs. By doing so, you can mitigate the use of unsanctioned apps and devices and put controls in place to ensure your organization is meeting data compliance and regulatory expectations.
Consider data retention in digital messaging platforms
The use of digital messaging platforms in the workplace presents challenges in data retention, especially for platforms that have auto-deletion settings. Ensuring that your organization has a clear understanding of how these applications store and retain data, as well as how it can be accessed, is also a critical component of preventing spoliation. Furthermore, when it comes to employee resignations, organizations must be proactive in setting up protocols to quickly and effectively preserving employee data should it be required for investigation.
Data retention and backup strategy in cloud-based applications
When it comes to cloud-based platforms and applications, effectively preserving digital evidence requires an in-depth understanding of its built-in retention policies for litigation holds.
For example, for Microsoft 365 (M365), a subscriber can access, extract, or delete data stored in Microsoft 365 during the term of an active subscription. If a paid subscription ends or is terminated, Microsoft retains subscriber data stored in M365 in a limited-function account for 90 days. After the retention period ends, Microsoft disables the account and deletes customer data.
Another thing to consider is that when using cloud-based tools and platforms, backup failure can be a common occurrence and can happen due to a number of reasons, from human errors to software update issues, network infrastructure failure and cyber attacks or threats.
Therefore, having a good understanding of your cloud-based platform’s retention policy, combined with a backup strategy and intelligent cyber security solutions embedded into your network infrastructure can go a long way in preventing data loss, as well as in being an integral part of any data protection strategy.
Successfully navigate your way to effective data retention and preservation in the hybrid workplace
Today’s hybrid work and technology are constantly evolving, and IT and legal departments must be able to keep up and stay ahead of the potential compliance and litigation risks.
IT professionals need to be aware of the limitations of application and platform retention policies, and implement data retention strategies and solutions such as extended backups with secondary storage options to prevent data loss and damage.
Legal and compliance professionals need to review their information governance policies to ensure they meet the challenges presented by hybrid work – and now is the best time to do this. You need powerful and agile eDiscovery tools and services that can evolve and scale along with your needs to ensure secure, efficient and defensible litigation preparedness.
It is also important to keep in mind that data needs to be protected through all stages of its lifecycle using advanced, end-to-end cyber security solutions to deliver comprehensive data protection for your organization.
Ready to get better security, control and oversight over your data? Get in touch with a Ricoh representative today to get started!
Recommended for you
 Articles
ArticlesEmpowering collaboration with meeting spaces
Today's hybrid workforces need integrated and secured workspaces designed to enhance virtual collaboration.
 Articles
ArticlesIntersection of print & information security
Information and data security involve more than secured networks and connectivity. Print, for example, is one often overlooked area.
 Articles
ArticlesConsiderations for security and printing
Explore top use cases and innovative solutions for devices, data, documents and user security.